Tag: VulnDB
-
Miggo, KEV, and FUD; They Still Don’t Get It

[If the name ‘Miggo’ is familiar to you in the context of my blogging, you are thinking about one I wrote titled “Miggo Security’s AI Slop & Potential Trademark Infringement” in July, 2025. That was more around ‘corporate’ culture and bad lawyering. This blog is different, pointing out how they don’t seem to understand KEV…
-
What Do 2025 CVE Numbers Mean? An Intro.
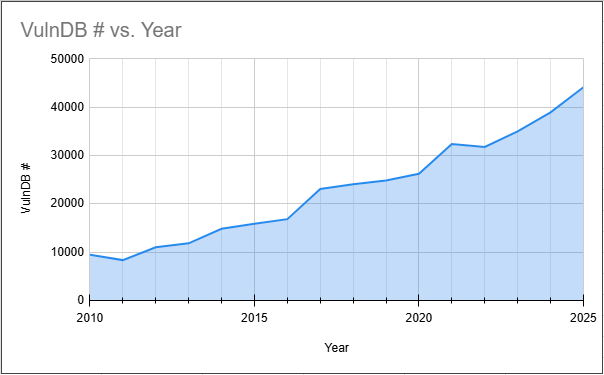
[This was originally my proposed introduction for Flashpoint’s 2026 Global Threat Intelligence Report. Due to the style of the report and covering a lot more intelligence sectors than vulnerabilities, only pieces of this were used. So I am publishing the entire original draft here for posterity.] The fact that there were over 48,000 CVEs published…
-
Bob’s “CVE Quality-by-Design Manifesto” – The Hit and Misses

Almost every time Bob Lord blogs, I feel the need to write a rebuttal to what is arguably abject stupidity and shortsightedness. One he published a couple days ago, titled “CVE Quality-by-Design Manifesto“, is missing several core concepts in the realm of vulnerability intelligence. While his overall point is certainly valid, the order in which…
-
Miggo Security’s AI Slop & Potential Trademark Infringement

On July 14, 2025, a relatively new security company named Miggo Security announced a new offering called VulnDB. Even for my casual readers you may have done a double-take thinking I just made a glaring error. No, not this time, it seems that Miggo made the glaring error. Apparently, rather than do a simple Google…
-
APT Naming Woes Redux (Bonus ‘DOJ’ Oops!)

One aspect of vulnerability intelligence is also doing a best-faith effort to track the threat actors that are using the vulnerabilities. While that information often isn’t published, when it is we should include it. For example, less than 1% of data breaches publish the vulnerability associated with the initial compromise, and that is often the…
-
“Secure” E2E Messaging Apps: More Than Meets the Eye
[This was originally published on RiskBasedSecurity.com.] Secure messaging apps, often touted as having end-to-end (E2E) encryption, have become extremely popular in recent years. This popularity has increased even more in the last two months, likely influenced by increased anxiety over the power wielded by “big tech” and endorsement by celebrated tech business leaders like Elon…
-
Why EVM Security Hasn’t Changed For More Than 15 Years
[This was originally published on RiskBasedSecurity.com in the 2020 Q3 Vulnerability Quickview Report. It was authored with Curtis Kang.] In our 2019 Year End Vulnerability QuickView Report, we presented a detailed history of public Electronic Voting Machine (EVM) vulnerabilities. We’ve seen little change to the overall EVM security picture since then. With the Presidential elections…
-
Electronic Voting Machines; That Old Redux…
[This was originally published on RiskBasedSecurity.com in the 2019 End-of-year Vulnerability Report.] Integrity is one of the cornerstones to both the concept and the practice of Information Security. We want to make sure that the integrity of the systems we use remains intact. It doesn’t matter if it is your smart watch, smart IoT device,…
-
Case Study: Third-Party Plugins
[This was originally published on RiskBasedSecurity.com in the 2018 Q3 Vulnerability QuickView Report.] Many people are familiar with content management systems (CMS), which are used in a variety of roles. Millions of people use them via hosted software such as WordPress.com and companies use them for blogging and knowledgebase systems. Historically, despite their wide deployment,…
-
Our Reports Clickbait? No. Click Here To Find Out Why…

[This was originally posted to the Risk Based Security blog (now 404 and no IA copy), with contributions from Jake Kouns.] Last week, we published our 2018 mid-year report that included an overview of the vulnerabilities that we have tracked and included in VulnDB. We highlighted a key takeaway from the report in the title:…