One aspect of vulnerability intelligence is also doing a best-faith effort to track the threat actors that are using the vulnerabilities. While that information often isn’t published, when it is we should include it. For example, less than 1% of data breaches publish the vulnerability associated with the initial compromise, and that is often the same with who was behind the compromise. Recently, while performing such work on VulnDB, I had to expand the threat actors associated with an entry. I am sure you are all familiar with APT-C-26 aka Red Dot aka Clasiopa right? No… how about Stonefly AKA Group 77 aka UNC2970? No… how about G0032 aka UNC4736 aka T404? Wow, what will it take for you to recognize I mean Lazarus Group! Because all of those, and a lot more, are designated names for the same group. Ironically, without a more familiar APT## designation from Mandiant apparently?
APT-C-26 (Storm-0530, DEV-0530, G0032, ITG03, TA404, UNC2970, UNC4034, UNC4736, UNC4899, UNC577, Lazarus Group, Appleworm, Group 77, Guardians of Peace, HIDDEN COBRA, Office 91, Red Dot, TEMP.Hermit, The New Romantic Cyber Army Team, Whois Hacking Team, NICKEL ACADEMY, ZINC, Diamond Sleet, Labyrinth Chollima, Onyx Sleet, Andariel, Silent Chollima, PLUTONIUM, H0lyGh0st, DarkSeoul, Stonefly, Clasiopa, Gods Apostles, Gods Disciples, Jade Sleet, ATK 3, SectorA01, Gleaming Pisces, Slow Pisces, NewRomanic Cyber Army Team, TraderTraitor, Temp.Hermit, Hastati Group (North Korea))
For a good summary of the general issues, please check Kevin Townsend’s article in SecurityWeek. While it is from 2021, I believe it stands the test of time so far. I only mention that because some other resources I later quote from less than two years ago do not. I understand many points I make in this blog are not new, but I want to highlight some issues and speak to problems that I haven’t seen others talking about, and offer my input on proposed solutions and add some thoughts on a solution of my own. Finally, I will end with a very recent, real-world example of where I believe a major mistake in conflating names has led to some serious confusion.
The Problems Today
From Wikipedia, “In biology, taxonomy is the scientific study of naming, defining (circumscribing) and classifying groups of biological organisms based on shared characteristics.” This is something that bothers me when companies call their naming schemes a taxonomy. While the term can mean “naming”, that is the most simplistic part of the definition. In reality, these companies should be striving to do a lot more than naming it like “defining and classifying .. based on shared characteristics” and more importantly, doing it publicly, the “shared” part.
There is a lot of talk in literature on this topic, of “a Rosetta Stone”, to help cross-reference names between intel shops. But this has a serious flaw in the first word in that three word phrase. There isn’t “a” stone, singular; instead there are over a dozen such stones and they all aren’t as complete in some fashion as another stone. That means these stone chiselers aren’t willing to do serious, time-consuming but essential work to help ease the burden for the rest of the world, which is sometimes understandable. The analogy also fails because of the problem of constantly adding to the stone and having to correct mistakes, which a stone does not lend itself to either.
So not only do we have all these distinct “taxonomies”, we have multiple “Rosetta Stones” and very few actual comprehensive attempts to map names. That means if we find reference to INSIPID SENATOR we have to look across a wide variety of resources only to determine that is actually a different designation for APT-D-UMB, COMPLACENT DRIZZLE, WARBLING MONOTONY, and eight other names.
There are arguments for each intel shop giving their own name to a threat actor or cluster, and I will get to the most compelling one later in this blog. Temporarily agreeing to that, we still have the problem where some shops up and rename all of the groups they are tracking instead of just moving to a new schema and leaving the old one as is, further increasing names to track. Based on STORM-####, and assuming there are actually that many thousand names tracked by Microsoft, they just created that many more thousands of names in one shot with the “DEV-1 becomes STORM-1” rename in 2023. At least the two designations are easy to track given the 1:1 relationship.
Next, for some unimaginable reason, we have companies that are basically glamorizing these criminals in the pursuit of their marketing. Trading cards?! You know that each group with a card has probably made full-size color posters of their respective cards and proudly display them in their homes or offices, right? The lack of cards certainly wouldn’t stop them from their criminal activity but it sure would make their bragging less impactful if they said “Yeah I am part of TOWERING DILDO” instead of “RAGING MACHO EXTREME” while holding up a fun trading card. You can market without resorting to this, so stop.
Prior Art
Not that our industry is good at providing solutions to begin with, but suggested attempts to fix this problem certainly tend to go in the wrong too, in my opinion. Spiceworks suggests:
“A good example is the MITRE ATT&CK Framework. Although it does reference names in certain instances, it also uses standard descriptors to detail threat actors and their tactics, techniques, and procedures (TTPs). So, no matter what you call it, if it’s enumerated with a MIRE (sic) ATT&CK ID it is easy to identify the threat and therefore highlight gaps in defenses. This standardized approach has quickly elevated the framework to a must-have tool in every security practitioner’s toolbox.“
ATT&CK may be a good framework (for now), but MITRE is certainly a bad example. Look at the Common Weakness Enumeration (CWE) project and see that MITRE demonstrates they will handle it poorly if given the chance. I assume because they need to justify funding each year, when MITRE ran out of classes of vulnerabilities, they started creating one CWE ID for a ‘cluster’ of other CWEs. If MITRE were to handle threat actor naming they would do the same thing in time I bet. Eight threat actor attribute IDs might all be associated with what is suspected to be SLURPING EMU operating out of New Dorkland, because some companies will not buy-in to MITRE’s framework. Then that cluster ID will just become yet another name for that group and added to a dozen or more “Rosetta Stones”. Spiceworks goes on:
“Particularly given the current geopolitical environment, which adds another dimension to cyber threat activity, this type of information is useful in the sense that it is a clear reference to their geography, which can give insight into their motivation.“
Written in 2023 and I can’t help but think this is not accurate. Look at all of the FIN / Spider / whatever-you-call the financially motivated groups? Jackal / hacktivists as well, are not exclusive to any one or ten countries. Look at all the groups from Russia and China and consider how different their motivations really are. How many ways do you want to skin the “espionage” potato here, at least for a bulk of them? Long before the term “APT” existed I was a pretty staunch and outspoken believer that it didn’t matter who they were or why they attacked; just secure the damn box already. For every dollar you spend trying to figure out the ‘who’, that is one more dollar of your tiny security budget not used to stop them from getting in to begin with.
As a reminder to some and a pointer to others, I wrote about the challenges of attribution back in 2010 in an article titled “InfoSec, Sun Tzu and the Art of Whore“. After the fifth paragraph I remind everyone that attribution may not be as straight-forward was it seems sometimes, and guessing to motives is not a good choice. It’s something to keep in mind as we frequently see misattribution to this day. Was it really a nation-state that launched a DDoS attack against Twitter/X, or was it a small hacktivist group with a botnet and the victim simply doesn’t understand the current state of botnets and their power? Worse, what if there are literally two relatively young people behind it along with misconfigurations on X’s side?
“The closest tool we have to a mythical Rosetta stone is an open-source threat tracking tool licensed under Creative Commons with respected contributors who are doing their best to address the problem.“
Jumping back to the Spiceworks blog, you are all bad and should be ashamed of yourselves! How many times do I have to read crap like this about some amazing resource, only to read and re-read a few times to make sure I am not overlooking something when in reality you don’t even link to it. This is what “not helping” looks like. And again, there is no single Rosetta stone; instead, there is a veritable rock garden of Rosetta stones that are all incomplete.

Turning to ClownstrikeCrowdstrike, they claim that their naming is based on “Nation-states perform espionage and are identified by their country of origin’s national animal such as BEAR (Russia) or PANDA (China)“. Great, now we should have a somewhat logical approach to naming unless of course attribution changes and you have to assign a new name because the animal doesn’t match up. In reality, this is well-cited and also absolutely absurd. Looking at their naming schemes, the markhor is the national animal of Pakistan, not the leopard. Per Wikipedia, “North Korea has no official national animal, but the mythological winged horse Chollima is taken to be a national symbol.” The Asiatic Lion is widely considered the national animal of Iran, yet somehow they got “Kitten” instead of “Lion” while giving Russia “Bear” instead of “Cub”.
Playing favorites on assigning animals Crowdstrike? Then they give Jackal as the name for hacktivist groups “looking to create political disruption“. At that level of motive, with enough to be named by Crowdstrike, they would hopefully be serious hacktivist efforts not target-of-opportunity web defacers. Yet hacktivists get an animal that is known for being opportunistic omnivores and scavengers (ideal for said defacers), when these hacktivist groups should perhaps get the more noble of animals instead. So it’s hard to take Crowdstrike seriously when they can’t get their own overly-simplistic taxonomy correct.
Storm, previously ‘Dev’ are Microsoft’s designations for reference. Mandiant uses UNC which tends to make sense, basically “unsub” until later identified (e.g. UNC123456). Most other threat intel shops tend to give their own arbitrary names, even though they may very likely know a group is already named. And please note that “Gods Apostles” and “Gods Disciples” .. seriously?! Quit giving them names like this. These groups should be given names like BADGER DEMENTIA and DILAPIDATED DILDO instead, so as not to glamorize them. MISP Standard has developed their own ‘RFC’ for naming guidance and it is anemic to say the least.
Even writing about named groups doesn’t age well for those searching for prior information. For example, Tara Seals wrote an article talking about how “grim threat actors get goofy monikers” and mentions “Fancy Bear is also called Pawn Storm, Sofacy Group, Sednit and STRONTIUM.” Just five years later this is so outdated that searching for a majority of names currently associated with the group will not find this article including UAC-0001, BlueDelta, GruesomeLarch, and more. Florian Roth’s article from 2018 says that “Off the record: by demanding a complete standardization you just reveal a lack of insight.” On the record, by demanding we accept the status quo, you don’t fully understand how companies could help with the problem, but refuse to, as too many use it for marketing rather than the greater good. Roth doesn’t even link to his own spreadsheet from the blog for some reason, despite it still being available.
Others have written articles more critical of the current naming scheme. For example, Max Smeets wrote in 2016 an article titled “When Naming Cyber Threat Actors Does More Harm Than Good“. Kunal Hatode wrote “Unleashing Chaos: The Consequences of Renaming Cyber Threat Actors” a couple years and makes a great point:
“Creating new naming conventions for threat actors can overemphasize the importance of attribution. While attribution is certainly important in many cases, it is not always possible or necessary. In some cases, it may be more important to focus on the actual tactics, techniques, and procedures (TTPs) used by a particular group rather than on their identity. By creating new naming conventions for threat actors, we risk putting too much emphasis on attribution and not enough on understanding the actual threat posed by these groups.“
Hatode goes on:
“Instead, we should focus on using existing naming conventions or request an independent body like MITRE to develop code names which has an aligned objective reach to the community and developing better tools and techniques for tracking and analyzing the activities of threat actors, while also addressing the root causes of cyber threats.“
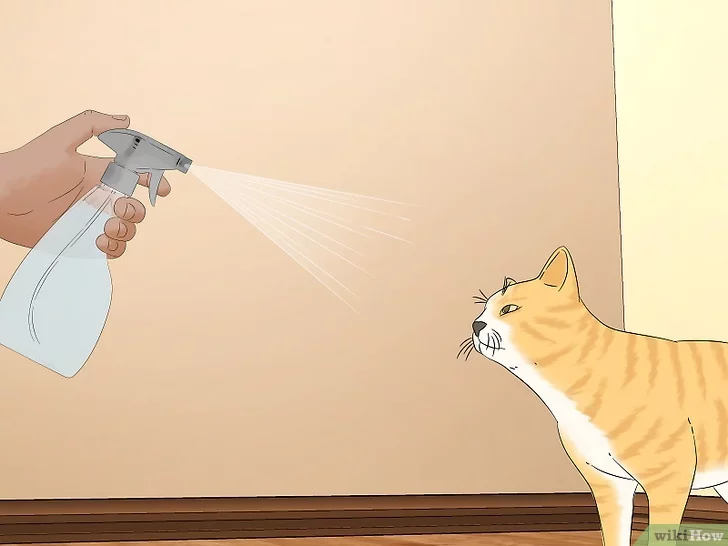
This was great right up until that MITRE comment! Sorry Kunal, you get the spray bottle.

MITRE has demonstrated they are not proficient in doing many frameworks as seen by the failures of CVE and the over-enumeration of the Common Weakness Enumeration (CWE). Additionally, there is a graveyard of old InfoSec-related projects and enumerations that MITRE has dropped completely and in general, MITRE takes on contracts with profit in mind. I am all for an independent, truly non-profit body being the arbiter of naming threat actor groups, using sane rules, and receiving enough data on IOCs and TTPs to help match “new” threats to existing names.
Now, to change gears and very briefly embrace the other side of the coin, I turn to Sergio Caltagirone’s article from 2016 titled “Names…Names Everywhere! The Problem, and Non-Problem, of Name Pollution“:
“What we shouldn’t do is to start using each other’s names – because, again, it’s not about the names. If you begin to use the names of others you start to take on their “analytic baggage” as well since you are now intimately associating your analysis with theirs. This means you may also take on their errors and mis-associations.“
This is actually the most compelling argument for letting the name sprawl continue and truly does have merit. But again, this article was from 2016, almost nine years ago, and has the same problem CVE did originally with a four digit limit per year. It isn’t forward looking and doesn’t speak to the increase in threat intelligence shops and ever growing pool of names. For those slightly outside that world, meaning in threat intelligence but not actively monitoring for this activity, the burden is on us to track and match all the names. Meanwhile those mentioning the groups after detecting them just have to give a couple cross-references, if that, before they go to the press. This is an unfair dynamic that shifts naming convention woes onto others.
Case Study of Name Pollution / Association Woes
‘Silk Typhoon’ has frequently been in the news lately, as they have become a more well-known and prominent threat actor group over the last years. ‘Typhoon’ tells us this is a Microsoft named group under their third taxonomy (STORM, DEV, now this scheme…) for a Chinese threat actor. On March 5, the U.S. Department of Justice formerly indicted “12 Chinese Contract Hackers and Law Enforcement Officers.. Including the ‘APT 27’ Group“. Later in the indictment it continues:
The APT27 group to which Yin and Zhou belong is also known to private sector security researchers as “Threat Group 3390,” “Bronze Union,” “Emissary Panda,” “Lucky Mouse,” “Iron Tiger,” “UTA0178,” “UNC 5221,” and “Silk Typhoon.”
Seeing the various names like this is to be expected, and refreshing to see the DOJ enumerate the designations. That refreshment hit a wall quickly upon seeing “Silk Typhoon” here because I didn’t think they were considered APT27. This is the kind of case that immediately makes me examine my associations because this is a murky situation and errors happen. What did I have before this indictment?
G0125 (ATK233, Silk Typhoon, HAFNIUM, Operation Exchange Marauder, Red Dev 13, timmy (China))
APT27 (G0027, TG-3390, Emissary Panda, BRONZE UNION, Iron Tiger, LuckyMouse, Budworm, Iron Taurus, Brown Worm (China))
You may immediately notice that there is zero overlap in my two group listings. So jumping back to DOJ’s list, let’s bold which I had associated with APT27:
Threat Group 3390, Bronze Union, Emissary Panda, Lucky Mouse, Iron Tiger, UTA0178, UNC 5221, and Silk Typhoon
UNC 5221 has one definitive reference that I can find today, from Mandiant, and does not associate them with any other groups. Malpedia lists UTA0178 and one other alias, Red Dev 13, which I have with Silk Typhoon, but Malpedia does not make that association either. That leaves the two names that are in contention, strongly suggesting that the DOJ did not get this mapping right. So let’s go to the big mappings and see if anyone else associated APT27 with Silk Typhoon.
- MISP Galaxy: Silk Typhoon, Red Dev 13, ATK233, G0125, Operation Exchange Marauder, APT27
- MITRE: G0027, Earth Smilodon, TG-3390, Emissary Panda, BRONZE UNION, Iron Tiger, LuckyMouse, APT
- Microsoft: Circle Typhoon, DEV-0322, APT6, APT27
I’ll stop right there because Microsoft uses the ‘Typhoon’ naming scheme in their taxonomy and does not call APT27 ‘Silk’, rather ‘Circle’ and further associates APT27 with APT6. To me, this means that the DOJ has made a serious error conflating two groups and done it on the world stage. This press release has led to news outlets covering and the bad association to go viral basically. Now, everyone in the threat intel world and beyond will have to live with this confusion. The only upside for me is I added a few more designations to my groups and got this section of a blog I had already begun weeks before the indictment.
Am I correct on all the above? I’d like to think so! But tracking APTs isn’t a core part of my job, so I may be missing here. The fact that I have been tracking them, as relates to the vulnerabilities they use, for almost a decade should tell you that even if I am wrong… there is a serious problem here.
Solutions?
Let’s say Caltagirone is correct, and the best thing is to let the names fly and just deal with an ever-increasing list of names. What options are there? Perhaps a CISA or NIST-run resource, that is simple with low overhead, that allows these companies to put their request for a new name along with their IOCs and TTPS. If any of those match, the system gently pushes back by showing how many IOCs overlap other groups. So if a company requests a new group WAILING DIAPER and provides 100 IOCs, they might get back 10 that match known groups. If nine match STUBBORN NEESON, the system suggests that may be the same group and indicates what company named the match and provides all other known names for that group. If a scheme is developed based on alphanumeric designations, not words, it would allow for a better representation and likelihood that groups are associated such as GRP-A500 and subsequently GRP-A500-1 and GRP-A500-2, indicating that the overlap of IOCs and TTPs is strong enough to associate them.
Basically, force these companies to attempt to use a common name, if the evidence is there. Our industry talks about cooperation and working groups and the greater good, then completely dismisses or drops it the minute marketing and profit are brought in. That has to stop, for that greater good we all want… right?

Leave a Reply