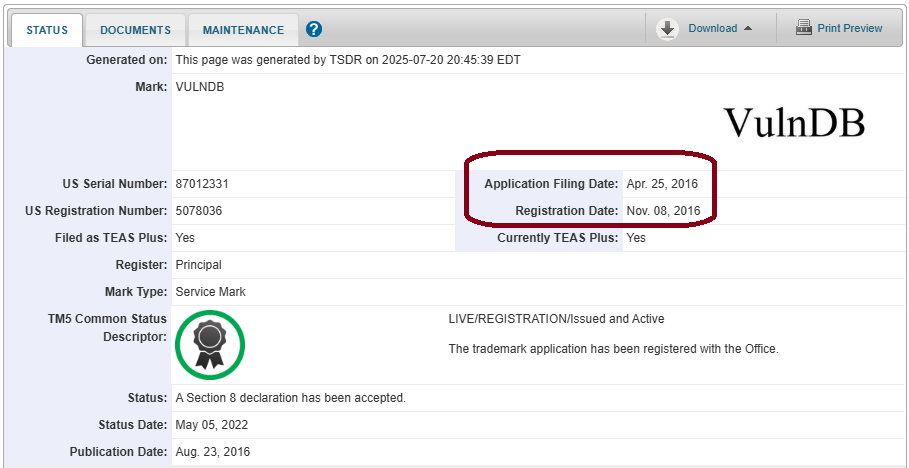
On July 14, 2025, a relatively new security company named Miggo Security announced a new offering called VulnDB. Even for my casual readers you may have done a double-take thinking I just made a glaring error. No, not this time, it seems that Miggo made the glaring error. Apparently, rather than do a simple Google search to see if “VulnDB” was already in use, they did not. Apparently, instead of a simple Patent and Trademark Office search to see if “VulnDB” was a registered trademark, they did not. Even a company that claims their offering uses so-called AI seems to have apparently forgotten to ask Gemini, Copilot, and ChatGPT “what is VulnDB” where two of the three even say who the actual offering belongs to (Flashpoint), albeit one is a bit outdated (saying Risk Based Security).

Reading the press release, the company markets on:
Powered by Miggo AI, this predictive VulnDB delivers real-time, actionable insights into emerging vulnerabilities in all types of applications (cloud-native, 3rd-party, and appliance-based).
You sure about that Miggo? When I looked after the announcement I checked and a recent Juniper vulnerability on CISA’s Known Exploited Vulnerabilities Catalog I did not see it in Miggo’s database. Neither did I see vulnerabilities in Cisco Identity Service Engine, Citrix NetScaler (CitrixBleed 2), Microsoft 365, and SQLite that are all being exploited in the wild. Those are fairly new but if you advertise yourself as “predictive” and “real-time“, being days and weeks late isn’t a good look. But really, I personally think it is a trash offering and all marketing buzzwords because when you look for Heartbleed, that too isn’t something I found in their database. From 2014. Exploited for at least nine years. A vulnerability in one of the most-used third-party libraries out there.
When they say this offering is “AI powered” and it delivers “real-time” insights, you might also be surprised to learn that their so-called AI seems extremely slow. Considering the press release says that this “deep context, seconds after disclosure, enables security and development teams to…” (my bold emphasis), it’s odd to me to see such a delay on a vulnerability disclosed almost three years ago. Worse, they list that vulnerability as not being exploited in the wild, where others say it has been.

Despite me pointing out the naming issue many days ago on LinkedIn in a reply to them, Miggo decided not to change the name and instead delete comments from myself and at least one other security researcher who pointed out some of the above. So at this point they know that “VulnDB” has prior usage, they opt not to change the name, and they apparently think they can just sweep it under the rug. Cool. Now they get this blog instead, and unlike that comment, they can’t erase this one.
In my opinion, this is just pathetic so-called AI slop, a half-assed offering, and their vulnerability database doesn’t live up to their marketing hype.
[July 22, 2025 Update: Miggo has deleted at least one more comment posted to a different announcement on LinkedIn. Trying to hide this is not going to work.]


Leave a Reply