[This was originally published on RiskBasedSecurity.com in the 2019 End-of-year Vulnerability Report.]
Integrity is one of the cornerstones to both the concept and the practice of Information Security. We want to make sure that the integrity of the systems we use remains intact. It doesn’t matter if it is your smart watch, smart IoT device, laptop, workstation, automobile, or an airplane. If it has a connection, bad people can do bad things to those systems, and the consequences can range from annoying to deadly.
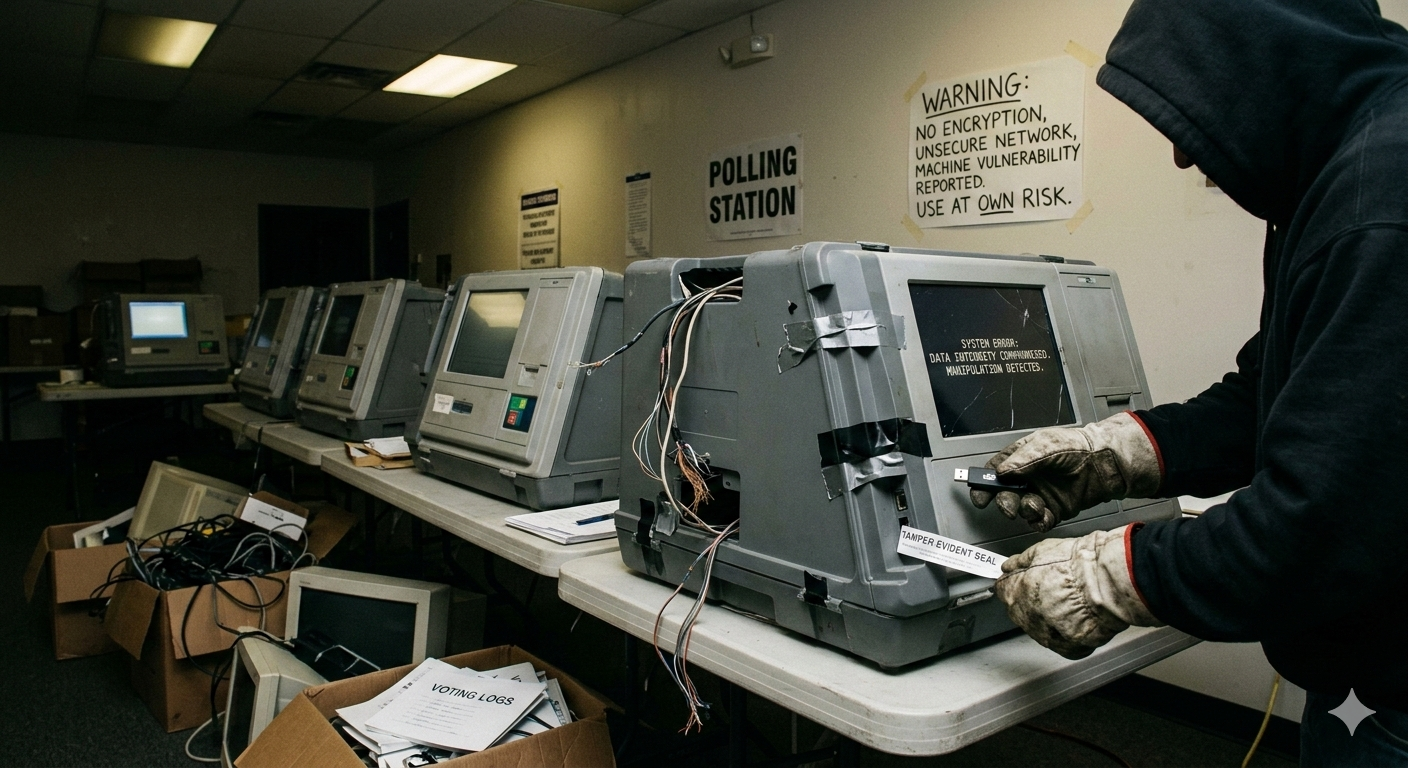
Overall, the word “integrity” has been a hot topic in 2019 and it will continue to dominate most of 2020. You can’t go more than a few minutes on social media without seeing something about politics, and more specifically, the next election. Whether it is the next county or presidential election, those elections are increasingly performed using “electronic voting machines” (EVMs) to tally the votes. As with any device that relies on code, there are vulnerabilities that can affect the system’s integrity, and you don’t want someone tampering with them. It doesn’t matter what politics or beliefs you subscribe to; the essence of democracy is that an election captures the will of the people.
A Severe Lack of Attention
Even though EVMs are instrumental in the democratic process, EVM security has received very little attention outside of InfoSec journalism. One of the most prominent journalists covering election security is Kim Zetter, who does a phenomenal job. Other than Zetter and Matt Bishop, an academic who has led teams that discovered EVM vulnerabilities and challenges the status quo, the only security researchers that seem to ‘sound the alarm’ have been Risk Based Security (RBS). Even before co-founding RBS, I took a specific interest in EVM security throughout 2009 in the context of formally cataloging their known vulnerabilities. While there were several academic papers that went into amazing detail in determining the flaws, they were lost to the general public because they are so complex and challenging to communicate. To me, this was a combination of the way academics approached vulnerability research, along with the ways EVMs fundamentally differ from other computers, such as their interfaces and singular purpose.
Despite the lack of attention, I was trying to highlight the potential impact of these vulnerabilities in 2012 saying, “Prepare to be scared for the coming elections.” Jump to 2016 and RBS was describing the situation as “an Old but Looming Threat” with 260 EVM vulnerabilities. In 2018, we again talked about the threat (now no longer “looming”, as concerns of foreign meddling saturated the news), with 292 EVM vulnerabilities documented. Hopefully we don’t sound like a broken record given the time between posts, but if there is a topic in computer security worth talking about, it is this one.
The Current State of EVM Security
As of this report, we stand at 302 documented vulnerabilities in Electronic Voting Machines and 96% of them do not have a solution available. To make matters worse, of those, only one vulnerability (0.3%) has a CVE ID assignment and is cataloged in the U.S. National Vulnerability Database. That’s right, just one. Even if election precincts have security processes or audit standards, or conduct vulnerability scans, they are likely based on policies, methodologies and scanners that rely on CVE for vulnerability intelligence. This means that election precincts won’t be aware of these issues because their security solutions won’t even know that there is an issue to begin with. There is no doubt that electronic voting machines with vulnerabilities have been used in past elections, and will be used again in the next election.
Currently, Election Systems & Software (ES&S) still sells their popular ExpressPoll tablet, which “gives poll workers a simple-to-operate device that reduces check-in and verification waiting time for voters, increases the accuracy of ballots issued and improves the Election Day experience for all.” Unfortunately, there are nine vulnerabilities known in those devices, none of which have a solution. Can it get worse? Sadly, yes. These vulnerabilities include default, hard-coded administrator credentials, no encryption for polling information, and ways for a voter to subvert the entire machine to manipulate votes. This isn’t a one-off case either. ES&S links to a blog touting that North Carolina certified their ExpressVote (which according to ES&S doesn’t have any published vulnerabilities) and also touts that their iVotronic device “currently serves more than 2.4 million voters” in the state. But despite their claim, that device has seventeen published vulnerabilities.
The Evidence is Damning
Regarding the EVMs, some skeptics say “that the system is accurate and safe for continued use”. This and other statements repeatedly tout the security, saying that experts test the systems every election. However, when one expert was called to examine a machine, that isn’t what he found. Instead, he presented damning evidence in a finding that suggested systems were tampered with, or potentially compromised fully. Even more concerning is that the system in question was tampered with again just before it was handed over to the FBI during an investigation.
Integrity
In 1818, Benjamin Franklin wrote in his memoirs the following quote which speaks to the cornerstone of democracy and the importance of EVM security: “…they who have no voice or vote in the electing of representatives, do not enjoy liberty, but are absolutely enslaved to those who have votes and their representatives.”
Integrity. It is a cornerstone of Information Security. One thing we’re sure of is that electronic voting machines, regardless of vendor, do not demonstrate that integrity is part of their design and implementation. They have hundreds of vulnerabilities, their systems are designed so there are little to no audit trails, and there are too many past cases of systems being tampered with. This should be of deep concern to every American.
Leave a Reply