Tag: Kim Zetter
-
Electronic Voting Machines; That Old Redux…
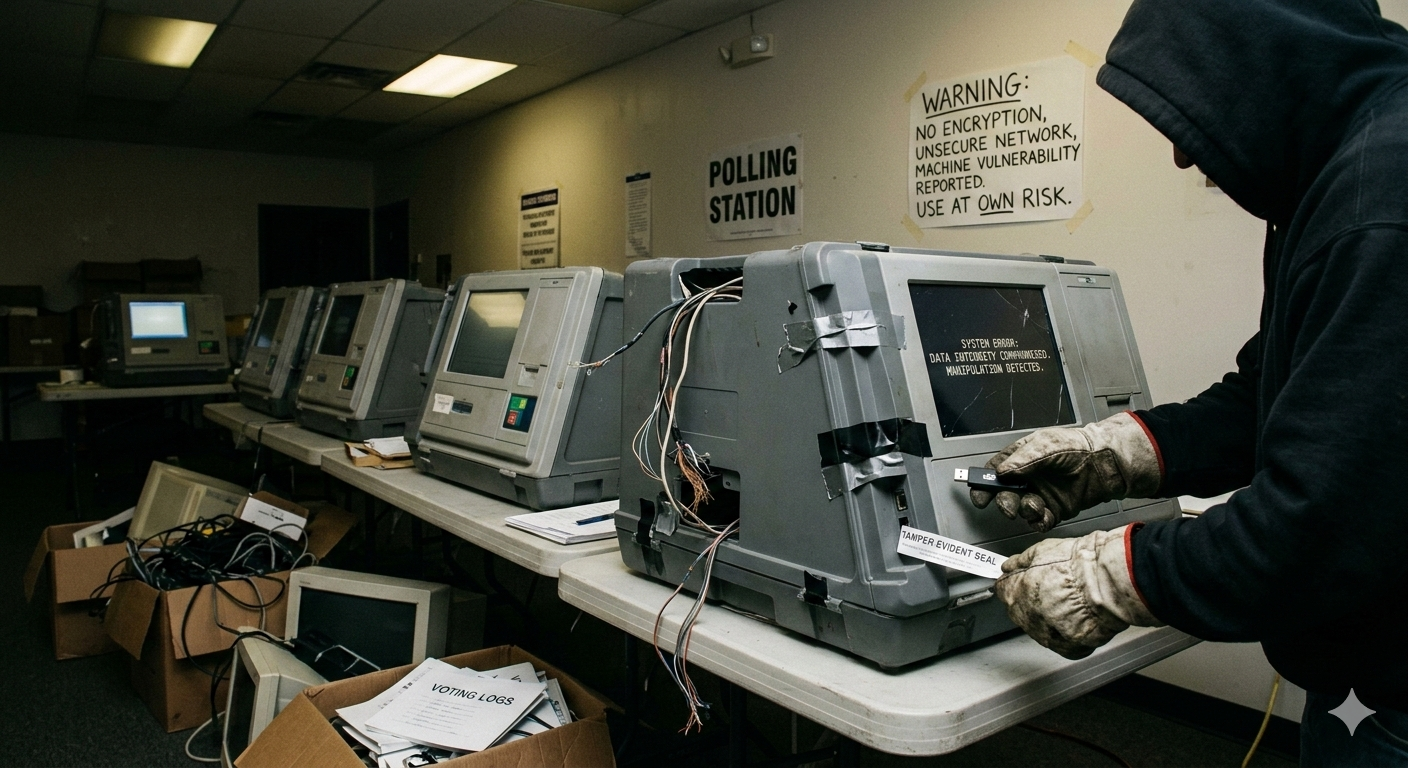
[This was originally published on RiskBasedSecurity.com in the 2019 End-of-year Vulnerability Report.] Integrity is one of the cornerstones to both the concept and the practice of Information Security. We want to make sure that the integrity of the systems we use remains intact. It doesn’t matter if it is your smart watch, smart IoT device,…
-
NTIA, Bug Bounty Programs, and Good Intentions
[This was originally published on the OSVDB blog.] [Note: This blog had been sitting as a 99% completed draft since early September. I lost track of time and forgot to finish it off then. Since this is still a relevant topic, I am publishing now despite it not being quite as timely in the context…