[This was originally published on RiskBasedSecurity.com in the 2020 Q3 Vulnerability Quickview Report. It was authored with Curtis Kang.]
In our 2019 Year End Vulnerability QuickView Report, we presented a detailed history of public Electronic Voting Machine (EVM) vulnerabilities. We’ve seen little change to the overall EVM security picture since then. With the Presidential elections in the U.S. somewhat now in the rear view mirror, it is as good a time as any to take stock of EVM security, and reflect on why so little has changed for the last 16 years.
A Healthy Amount of Skepticism
We’re not in the business of speculation, and maybe to your dismay we don’t plan to draw conclusions on foreign interference during the November elections.
However, we do plan to continue to shine a spotlight on EVM security (or the lack of it) for several reasons. First, there’s been little progress in closing known vulnerabilities in order to better secure the machines. Second, there is no way to audit many vulnerable machines, to even detect if it has been digitally tampered with.
The reality is that EVM security is far from perfect. Yet, despite the obvious concerns we have seen some patterns suggesting that the EVM vendors may not be taking their security duties as seriously as they should.
The Patterns We Have Been Seeing
At Risk Based Security we know it is important to know which of your vendors care about security, and we shine a light on that with our extensive vulnerability and data breach intelligence. Unfortunately, EVM vendors often do not seem particularly willing to embrace transparency, despite the important role that their products play in national security and democracy. Compiling sources and research, there are several key factors that contribute to overall staleness in EVM security.
The Vendor Mindset
Prior to the election, on January 9th, 2020, witnesses including the CEOs for ES&S, Dominion, and Hart InterCivic testified before the House Administration Committee, telling lawmakers that they had seen no evidence of election system tampering. However, when asked by Rep. Mark Walker of North Carolina to rate themselves between 1-10 on their security practices, each CEO carefully avoided giving a straightforward answer, instead saying that they are doing “everything they can.”
But what exactly does that mean? There aren’t many open examples of the measures EVM vendors take in securing these devices, but there are many examples of those vendors doing what they can to limit vulnerability reporting. The recent example of Voatz attempting to influence legislation involving the Computer Fraud and Abuse Act (CFAA) exemplifies the EVM mindset.
To summarize their Amicus Curiae, Voatz favors narrowing the CFAA to restrict independent researchers, stating that they believe open research to be harmful and a waste of tax dollars. Instead, they insist that “necessary testing and research” be done only by authorized parties, such as bug bounty programs and private consulting firms.
Voatz, along with many other EVM vendors, are designated as “critical infrastructure” by the Department of Homeland Security, so ensuring that these devices are secure should be a no-brainer. Although bug bounty programs play their part, there are concerns within the security community about relying exclusively on this approach. Those within the industry know that corporations using these programs sometimes push NDAs on participants, which can be seen as an attempt to buy a researcher’s silence if they get paid for reporting a vulnerability. Even if a researcher agrees to sign, it doesn’t guarantee that the vulnerability will be fixed by the vendor.
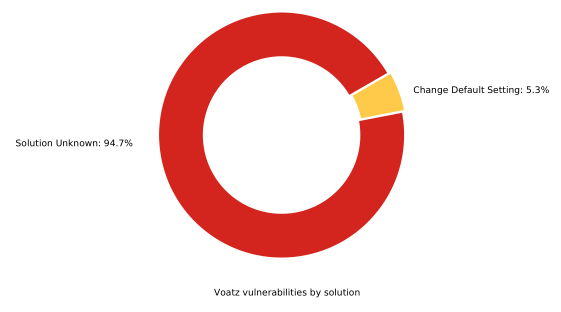
Insistence on limiting who can report a bug can give the impression that vendors are more interested in preventing people from disclosing vulnerabilities in their products than they are in working with researchers to make their products secure. Data within VulnDB shows that in Voatz’s case, numerous vulnerabilities within their product have been reported since 2013 – in fact one has a CVSS score of 10 and is considered to be remotely exploitable. However, despite the considerable passage of time, a solution is still not known.
Another example of the EVM vendor mindset is the official ES&S Security Test Report produced by Coherent Cyber. Multiple vulnerabilities were found throughout ES&S’s main line of products that could allow an attacker to obtain the highest privilege levels, enabling remote access into the system. According to one of the analysts who participated in the report, once ES&S was aware that the evaluation was taking place, they were “appalled” that his team would follow their own testing plan and not ES&S’s own preferred plan. Despite Coherent Cyber finding these vulnerabilities, ES&S was unwilling to work with them and informed Coherent Cyber that “they had their own team and were not interested.”
But isn’t it the duty of a red team to simulate an aggressor? Would an attacker play nice and follow the official testing plan, or would they take advantage of a vulnerable device any way that they could? Malicious attackers have a tendency to disregard safe spaces or play by “the rules”.
Domination of the Market and Form Over Function
Another key factor is the dominance of the EVM market by a small number of vendors, primarily ES&S, Dominion, and Hart InterCivic. While Coherent Cyber’s report should have aroused suspicions regarding the security of the devices provided by these companies, it has not stopped the government from continuing their contracts.
One of the main explanations as to why this is the case comes from the state’s involvement in the voting process. The responsibility of conducting and maintaining elections falls upon the states, who then often delegate responsibilities for voting machine selection, vote tabulation, and result validation to specific counties.
As such, counties will purchase machines that are either well-known in the market (like ES&S) or older, “affordable” machines that still function. Most of the time, these affordable machines are nearly ten years old and are from defunct vendors that have been bought out by the above mentioned EVM vendors. They are repackaged, but oftentimes still run on original hardware and software. Coherent Cyber reported that some devices like the ExpressVote, DS200, and DS850 have been found to run on Windows 7, despite Microsoft ending official support on January 14, 2020. News outlets have reported that these machines were used in the November 2020 U.S. Presidential election.
Many states and counties still rely on these old machines because the emphasis is placed on functionality over security. In fact, the Chairman of the Election Assistance Commission has arguably gone so far as to advocate the use of older machines:
“Those systems are very old. But they are more like the fact that if you have a classic car, to maintain that classic car, you change the oil, you change the brakes, the tires — that car will continue to function well. What you want to do is make sure that the classic car continues to run well. That is the same thing with voting systems.”
-Thomas Hicks, Chairman of the Election Assistance Commission
This analogy is flawed, because it neglects potential security implications. The issue at hand isn’t whether these machines will function, the concern is whether a thief can break in. Sure, the brakes and tires may work, but what about the locks? Depending on how old the car is, if someone is looking to break in, they might only need a clothes hanger. In cyber security terms, breaking into old systems is literally child’s play as we saw at Def Con 2018.
“Strict Security Protocols”
The bottom line is that EVM machines are vulnerable and have many documented, unpatched vulnerabilities. Our own research has revealed that there are 302 documented EVM vulnerabilities and 96% of them do not have a solution available. Unfortunately for the counties responsible for patching and securing these devices, only a single EVM vulnerability has been assigned a CVE ID. When lawmakers are confronted with these and similar findings, they often provide assurances to the public that these systems are “safe” and cite inherent security protocols. However, when these claims are investigated it turns out that the security measures they cite are not sufficient.
In Virginia, the “worst voting machines” of all time were used between 2003 – 2015 and were riddled with all sorts of problems including users being able to connect to the machines using cellphones. But when pressured, Virginia officials at the time told voters that the systems were “safe” due to “strict security protocols” and continued their use for seven more years.
The “strict security protocols” cited by these officials turned out to refer to the machine’s Wi-Fi network password. That password was “abcde” and was cracked by the FBI in two minutes. The simple existence of a password, despite its inadequacy, was enough to check the box for lawmakers. It has a password? Then it is secure. It’s secure? Then this device is safe. Is the situation any different today? Is it possible that current security concerns are dismissed on similarly weak logic?
Although the specific WINVote machine in this example is discontinued as of right now, it doesn’t change the fact that this insecure device was used for many Virginia elections and the thought process that permitted their continued use may still persist. Machines known to be vulnerable are still in wide circulation across the U.S. and they are being defended by politicians under the same pretenses as the WINVote machines. Sure, these machines may have passwords and “security protocols” in place, but that doesn’t mean that they are effective. In the HBO documentary, Kill Chain: The Cyber War on America’s Elections, the security PIN for the TSx machine was revealed to be “111111”, and the pin before that was “111.” Does this sound familiar? These TSx machines were reported to be used by several counties in 2020 elections. Assurances of security protocols do not make a vulnerable machine secure.
That Old Redux
We had hoped that the topic of EVM security would be resolved, or at least that substantial progress would have been made before the recent election (and the previous one), but there have been no substantial changes, despite the discussion being alive for over a decade, we are not very hopeful that it will be fixed anytime soon. To reiterate, Risk Based Security is not saying that the 2016 nor the 2020 elections have been digitally compromised, as there is no evidence showing such and that is outside the scope of this research. What we are saying is that EVM machines have been and continue to remain vulnerable. Given what we know about the past and present, we sincerely hope that real progress can be made to increase transparency with EVM vendors and harden our vital democratic processes.
“Those who cannot remember the past are condemned to repeat it.”
-George Santayana

Leave a Reply