Tag: Vulnerability Statistics
-
Miggo, KEV, and FUD; They Still Don’t Get It

[If the name ‘Miggo’ is familiar to you in the context of my blogging, you are thinking about one I wrote titled “Miggo Security’s AI Slop & Potential Trademark Infringement” in July, 2025. That was more around ‘corporate’ culture and bad lawyering. This blog is different, pointing out how they don’t seem to understand KEV…
-
What Do 2025 CVE Numbers Mean? An Intro.
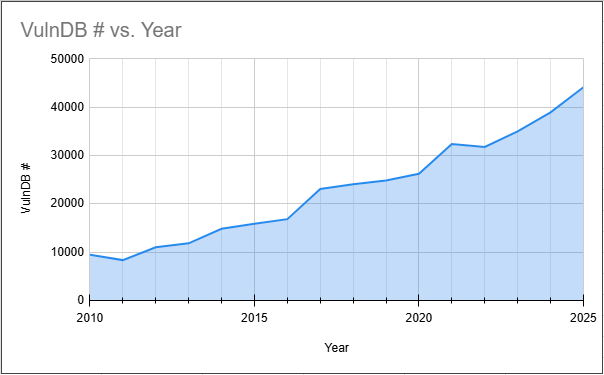
[This was originally my proposed introduction for Flashpoint’s 2026 Global Threat Intelligence Report. Due to the style of the report and covering a lot more intelligence sectors than vulnerabilities, only pieces of this were used. So I am publishing the entire original draft here for posterity.] The fact that there were over 48,000 CVEs published…
-
Reporting on the IBM 2025 Report

On April 16, 2025, IBM posted their X-Force 2025 Threat Intelligence Index. Like many reports of this nature, it covers a wide variety of aspects relating to threat intelligence. Of course, one of those aspects is vulnerability intelligence and this report has a section for that. You are reading this so you can guess where…
-
VulnCon Day 2 Errata & Taking Ben Edwards to Task

[4/13/2025 Update: See very end, below last image, for an amusing update.][2/19/2026 Update: See very very end for an amusing update, yet positive!] Today was the second day of VulnCon 2025, a conference whose stated purpose is “to collaborate with various vulnerability management and cybersecurity professionals to develop forward leaning ideas that can be taken…
-
Has CWE Jumped the Shark?

The Common Weakness Enumeration (CWE) is a MITRE run, community-developed list of common software and hardware weaknesses (Wikipedia Page). The project defines a “weakness” as “a condition in a software, firmware, hardware, or service component that, under certain circumstances, could contribute to the introduction of vulnerabilities.” This taxonomy has several uses but they tend to…
-
Known Exploited Vulnerabilities (KEV) Thoughts – Part Two

This is part two of my thoughts on Known Exploited Vulnerabilities (KEV), and where it gets a lot more interesting! Please see the first blog before starting here. Automation / Eagerness To Add Reading vulnerability disclosures can be a grueling mission full of frustrations. Poorly written advisories, missing technical details, and errors make the life…
-
Vulnerability Forecasting Technical Colloquium – A Few Thoughts

[I wrote this on September 21st, but apparently forgot to ultimately move from GDoc to Blog. I suspect because it really needs to be cleaned up as it is my first draft. Rather than do that, since the event has passed, I will just backdate instead. This blog was actually published December 28, 2024.] Part…
-
Will the Real 300,000 Stand Up?

On September 27, 2022, Flashpoint’s VulnDB hit the 300,000th entry added to the database. Think about that and .. wow. I started the adventure of collecting vulnerabilities around 1993, back when it was all flat text files, and my hacker group used a FILES.BBS file as an index, pointing to many hundreds of other text…
-
Microsoft SIR and Vulnerability Statistics

[I wrote this for my day job back in February, 2017, but it never got posted. Including it here for reference.] The notion of expertise in any field is fascinating. It crosses so many aspects of humans and our perception. For example, two people in the same discipline, each with the highest honors academic can…
-
Let’s Talk About 0-days

[This was a first draft of an article to be published on the Flashpoint Threat Intel blog. Ultimately, parts of it were adopted for a different blog but the original remains considerably different. Curtis Kang contributed significantly to the finished blog below.] Zero-days (0-days and other variations) are exploitable vulnerabilities that the general public is…