On April 16, 2025, IBM posted their X-Force 2025 Threat Intelligence Index. Like many reports of this nature, it covers a wide variety of aspects relating to threat intelligence. Of course, one of those aspects is vulnerability intelligence and this report has a section for that. You are reading this so you can guess where I am going. It’s been a while since I have taken vulnerability reports to task, largely due to Secunia going away which removed the burden of calling them out every year. I am pretty sure this is the first time I have called IBM out, but here we are!
Let’s begin…
Also, of note, the number of vulnerabilities has increased rapidly over the past eight years and grown threefold. This could be attributed to many factors. Perhaps the most likely is a growing reliance on shared cloud infrastructure and services.
I’ll disagree there, because of the over 300,000 unique vulnerabilities cataloged by IBM, how many are in cloud infrastructure and services? Less than half a percent of CVEs issued this year are in cloud or services. While the number of assignments in said services is increasing, it is trivially small and bordering statistically irrelevant. The actual reasons for the increase in vulnerabilities are quite apparent, that just isn’t one of them.
In the “Growth of vulnerabilities, weaponized exploits, and zero days” section, the first chart shows that in 2024 there are considerably more than 300,000 CVEs:
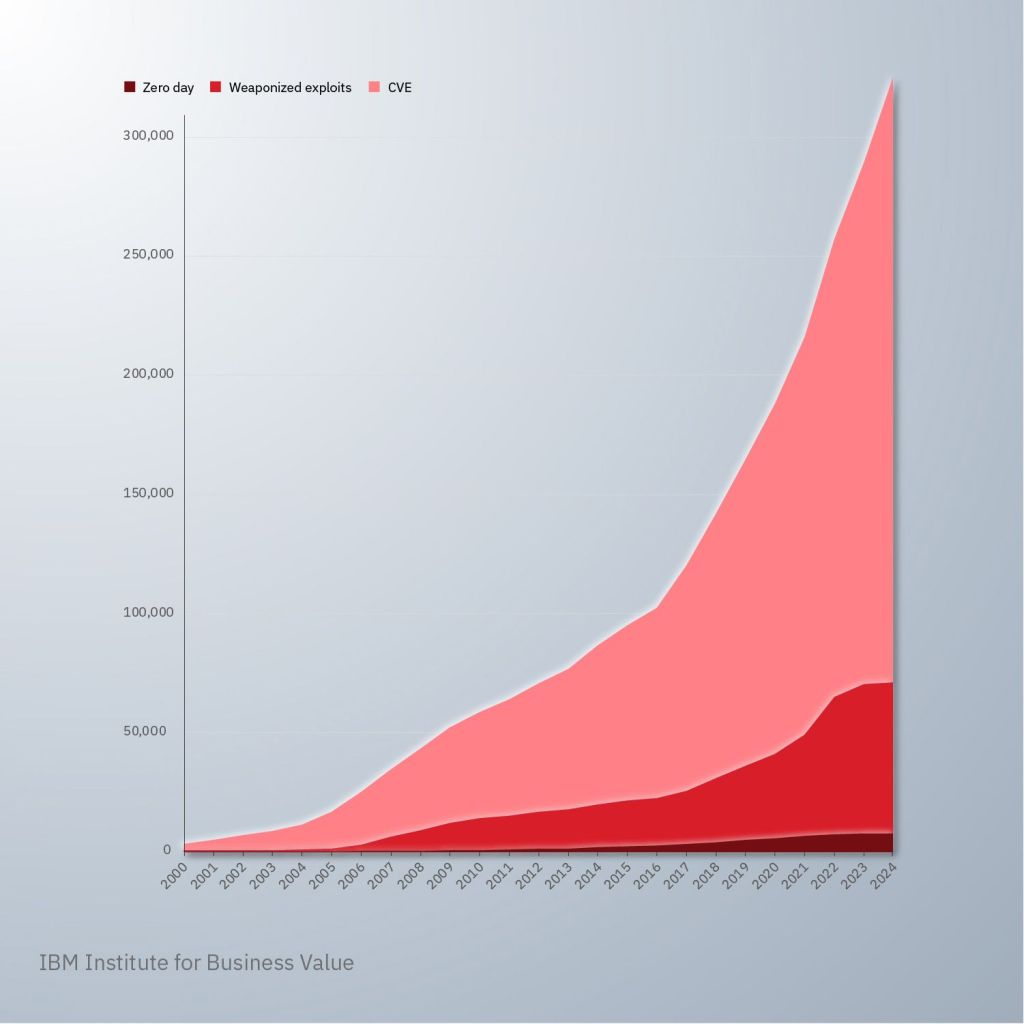
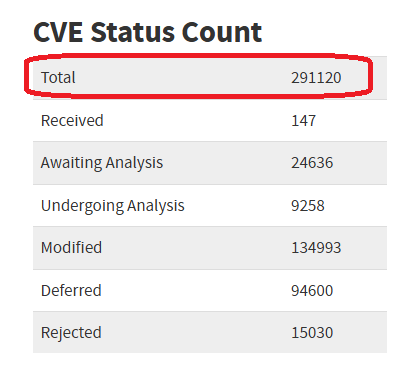
However, as of April 22, NVD only showed a total of 291,120. That is a difficult discrepancy and hard to imagine how it was overlooked.
Before we move on, we must also observe that this chart’s caption says “Number of observed vulnerabilities in the wild“, while the legend shows the chart tracking “Zero day“, “Weaponized exploits“, and “CVE“. There is no legend category or color for “Known Exploited Vuln”, so the caption’s use of “in the wild” is certainly confusing.
MITRE Corporation maintains a publicly listed catalog of CVEs, and the CVE list feeds the US National Vulnerability Database (NVD) which quickly enriches each CVE once it has been published.
I think someone has been on vacation since October, 2023. It’s hard to imagine anyone working in the vulnerability space being oblivious to the ongoing news about the “NVD slowdown” that has recently turned into the “NVD near-stoppage”.

A zero day vulnerability refers to a flaw in an operating system of software that leaves a system open to attack until the developer finds out and releases a fix.
I think this would be the fifth definition of a “zero day” I have heard in the last year alone. This definition is simply not true in that a zero day does not have to be in an operating system. You can ask all the companies that have been popped by vulnerabilities in Google Chrome, Microsoft Edge, and Apple Safari for example. Then talk to those popped by products made by Ivanti, Fortinet, Juniper, VMware, Palo Alto, Apache, SonicWALL, Kerio, QNAP, WhatsApp, Cleo, and the list goes on.
Conclusion
The vulnerability section of the report isn’t terribly long, but a couple of these are fairly egregious errors. I really don’t like calling out IBM because the X-Force database has been around longer than CVE and done a better job cataloging vulnerabilities through all those years. I can only hope that the current X-Force staff will be more diligent when publishing charts and numbers like this as it reflects poorly on the team, and IBM. My sincere and long-standing offer of doing free proofreading services for vulnerability reports is still on the table.

Leave a Reply