On October 3, 2024, Aquasec published a report about newly discovered malware named “perfctl”, targeting Linux servers. In it they cite the malware taking advantage of misconfigurations, as well as attempting to “exploit the Polkit vulnerability (CVE-2021-4043) to escalate privileges.”
Only problem is that CVE-2021-4043 isn’t “the Polkit vulnerability”, which in itself is problematic since there are almost a dozen vulnerabilities in polkit. What they are trying to refer to is a polkit vulnerability dubbed “PwnKit” and assigned CVE-2021-4034. Note the transposition of 34 to 43 in Aquasec’s report. Here we are 25 days later and the CVE ID hasn’t been fixed, which is telling. Once I alerted them to the typo, they were quick to update it which is great to see!
How is it that no one has apparently pointed this error out to them, or if they have, why hasn’t Aquasec fixed it? I Tweeted to them today in case no one else had and they fixed it promptly. In the past I have pointed out how CVE typos can cause a lot of confusion and cause security teams to waste precious time trying to figure out if the issue impacts them. This problem is exacerbated when news outlets copy the incorrect ID from the original source and don’t check them. Even worse when said outlets block me on Twitter and haven’t seen my corrections.

It should be no surprise that other articles and sites also incorrectly reference CVE-2021-4043 (polkit). Where this gets even more confusing is due to CISA adding CVE-2021-4034 (GPAC) to their Known Exploited Vulnerabilities (KEV) catalog four days prior to the Aquasec report. What are the odds of a NULL Pointer Dereference (NPD) vulnerability, traditionally only impacting availability, being used for local privilege escalation in the wild three years after disclosure, and just four days from the Aquasec report? I suspect the odds are pretty low, so I reached out to CISA for confirmation.
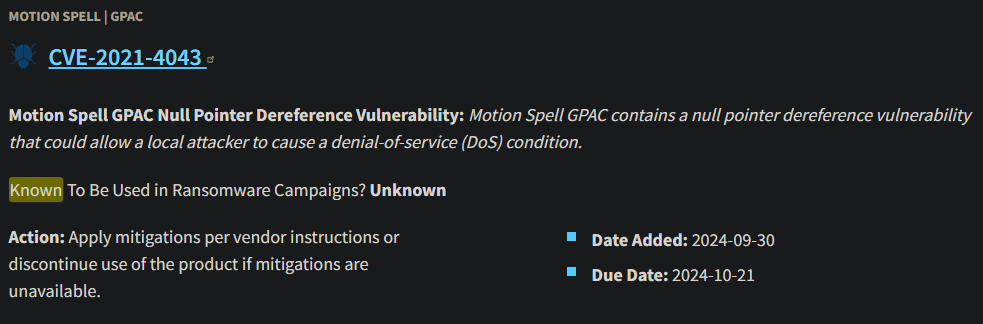
- 2024-10-28 – Contact CISA
- 2024-10-29 – CISA replies: “Your request has been forwarded to the appropriate office.”
- 2024-10-30 – CISA resolves case w/o comment. CVE-2021-4043 still present on KEV
- 2024-10-30 – I request case be re-opened.
- 2024-11-07 – CISA replies saying KEV updated. I verify CVE-2021-4043 no longer present.
- 2024-11-07 – CISA resolves case.
So here’s a case of a typo CVE causing a lot of wasted time for organizations trying to remediate it per CISA BOD 22-01 guidelines.This is also an interesting contrast to the rigorous standards for inclusion in the KEV that were presented at VulnCon 2024, as covered in my blog on the talk. I suspect that the CISA KEV team is understaffed and facing an incredible backlog of vulnerabilities to examine, which may have led to this. Note that I am not pointing fingers at anyone as we all make mistakes, especially typos. This just serves as a reminder that when it comes to CVE IDs, ensuring accuracy can be critically important.

Leave a Reply