[This was originally published on RiskBasedSecurity.com.]
Companies that once said they would not pay for vulnerability information seven years ago, have been steadily expanding their program to pay for more and more vulnerability information and recently made Edge bounties permanent.
Service-oriented companies like Uber, that rely on a significant amount of user interaction and transactions via mobile apps, also utilize bounty programs. Surprisingly many industries, even the U.S. military have entered the bug bounty game, as the Department of Defense (DoD) announced in 2016 their own vulnerability bounty program, to be run through HackerOne.
As can sometimes happen with high-profile bug bounty programs such as United Airlines in 2015, they can come with a bit of drama. The initial announcement of the DoD program faced some turmoil. According to the DoD’s own press release, “participants in the bug bounty will be required to register and submit to a background check prior to any involvement with the pilot program.” An Ars Technica news article goes on to enumerate more requirements, citing the HackerOne project for the bounty:
- You must have successfully registered as a participant through this security page.
- You must have a US taxpayer identification number and a Social Security number or an employee identification number and the ability to complete required verification forms.
- You must be eligible to work within the US; meaning you are a US citizen, a noncitizen national of the US, a lawful permanent resident, or an alien authorized to work within the US
- You must not reside in a country currently under US trade sanctions.
- You must not be on the US Department of the Treasury’s Specially Designated Nationals list [a list of people and organizations identified as being involved with terrorism, drug trafficking, and other criminal activities].
Interestingly enough, when originally viewing the HackerOne DoD Bounty page (dead link) after the announcement it showed:
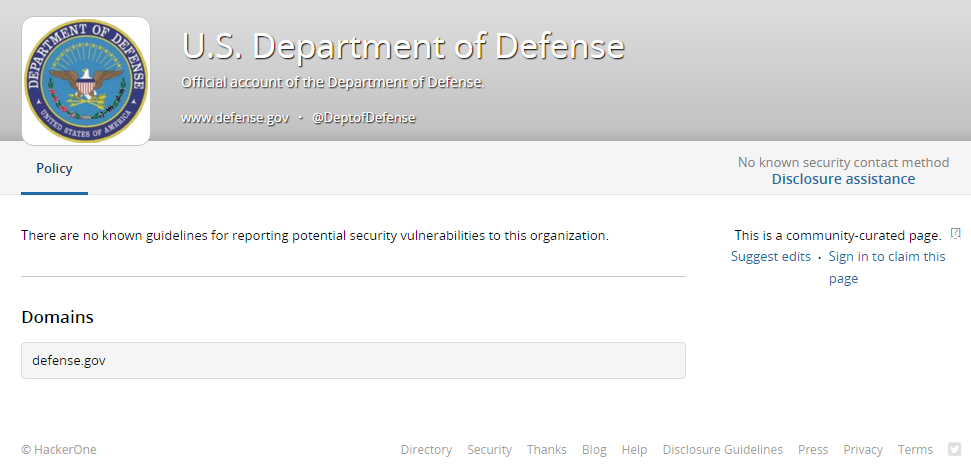
This type of confusion and lack of guidelines can cause a serious lack of trust among security researchers, who are notoriously paranoid, and often for good reason. For a program that the DoD describes as “innovative“, the lack of organization coupled with the registration requirements was concerning for many.
While the excitement of launching a bug bounty can lead to rushing implementation, it is very critical to be prepared and have clear guidelines in place from the very beginning. To be clear, the page has now been updated and provides the expected guidelines and other information. Interesting enough there are also some Response Efficient metrics that are posted publicly on the Hacker One bounty page. You can see that their average first response is three days, but it does take approximately four months on average for resolution. The continued debate on vulnerability disclosure also even exists in the Bug Bounty world as well.

Over the past few years, almost in-line with the increase in bounty programs increasing, we’re seeing more open sales of vulnerability information, as well as the information obtained by using those vulnerabilities. An article from mid 2016 in The Register cited Dell SecureWorks research that boiled down hacking activity into a menu-style offering:
- Banking credentials are sold for between 1% and 5% of the account balance.
- American Express Cards fetch $30, towards the upper end of prices for plastic card credentials, which start at $7 and rise depending on the type of card and the amount of associated data offered for sale.
- DDoS (distributed denial of service) attacks can be contracted for as low as $5 an hour, the same price as remote-access trojans.
- Angler exploit kits – a common hacking tool that’s used to sling malware from compromised or hacker-controlled websites – are licensed from $100.
- Crooks are also expanding their offerings with a greater range of products, including ATM skimming devices for $400 or less.
- Hacking a corporate email account costs $500 per mailbox, about four times the price of hacking into a Gmail or Hotmail account ($123).
Even on social media, users are becoming very open about their hacking activity. This includes the rather benign poking at notable media characters like Edward Snowden, and computer security professionals such as Kevin Mitnick.

The same person, @1×0123 on Twitter (account now suspended, so links are 404 but kept for the record), announced the compromise of naughtyamerica.com with 150,000 accounts and plaintext passwords, an unnamed nasa.gov system with remote access, implications that the New York Times web site has an SQL injection vulnerability, and the Los Angeles Times web site has a remote vulnerability that allows full access.
If that wasn’t enough, consider this was apparently one person and they also announced their own exploit market, to “improve safety & security products”. This comes full circle thinking back to the Department of Defense’s bounty program announcement, and the likely requirements. The same person also demonstrated a couple cross-site scripting vulnerabilities on Pentagon web sites.
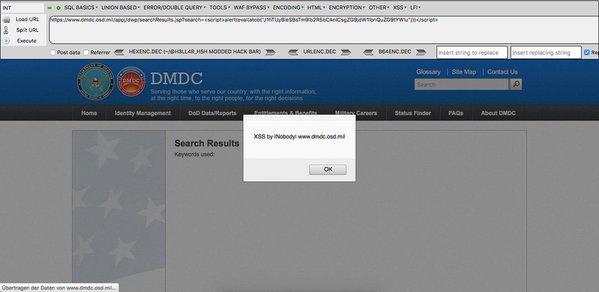
Since the initial DoD program, there have been more government bug bounty programs launched and or expanded. In January 2017, the U.S. Army launched a bounty and the U.S. Air Force launched a bounty-based contest for a given period of time. While the Army program seems to be part of the broader Hack the Pentagon initiative, no signs yet that the Navy, Marines, or Coast Guard have started a bounty program. Additionally, it is interesting to note the number of valid reports as compared to the payout for the Hack the Pentagon bounty:
Out of all the submissions, 138 were found to be “legitimate, unique and eligible for a bounty,” and resolved according to Defense Secretary Ash Carter. Those vulnerabilities earned $75,000 in total bounty rewards, paid promptly by HackerOne at the conclusion of the program.
That means the average payout was $543.48 and the total program payout of $75,000 was only 0.005% the cost of some military ordinance. Formal bug bounty programs are largely considered to be on the side of good and the domain of whitehat hackers, and increasingly considered “worth the risk”. It is important to note there is also a steady rise in their counterparts (as always, take commentary on the sales of exploits with a grain of salt).
More exploits, and the fruits of their use, are being sold on the open or black market to the highest bidder. Every day, RBS hopes that more data comes to light about these sales, even if in the past. We have been following the U.S. Government foray into the bug bounty world closely and have been pleased to see the continued expansion. It does beg the question as to how many other countries will view the U.S. results as a success and also begin to create programs as well.
Recently, the UK Government announced they were working with Katie Moussouris from Luta Security on their first vulnerability coordination pilot. Meanwhile, tracking vulnerabilities and the subsequent data breaches, continues to prove to be a healthy challenge. There has already been over 10,500 new vulnerabilities and more than 2,200 data breaches reported in 2017. Software vulnerabilities and the ‘businesses’ they create are not going away anytime in the near future. Organizations of all sizes in all industries need to address network protections and focus the necessary resources on vulnerability discovery and remediation.

Leave a Reply