Late last night, Steve Ragan published an article on the CSO Salted Hash blog titled “Company behind the Badlock disclosure says pre-patch hype is good for business“, immediately taking SerNet to task over their handling of the disclosure so far. One of the more telling parts of his article came during a conversation between Sean Sposito and Johannes Loxen, who registered the Badlock domain, in which Loxen said something about the vulnerability and then promptly deleted the Tweet:

Loxen’s comment appears to confirm that the vulnerability will allow a remote attacker to gain administrative access to the targeted host. Along with other clues, odds are still high that the issue will be independently discovered, potentially leading to serious headache for administrators. That leads into another interesting point that should be considered. While we know that Samba and Microsoft will be issuing patches in the coming weeks, we are also pretty confident that this is a flaw in the SMB/CIFS protocol, or in their implementation of it. If these two vendors implemented the protocol in a fashion that led to this issue affecting them, it is reasonable to assume that any other vendor implementing the protocol may do the same. That prompted us to dig around for other vendors and products that use it. Fortunately for us, Wikipedia made this very easy as it has a list of such vendors and products. Other software and vendors of note that may be impacted by Badlock, and who may find themselves scrambling when the details are published as they were not part of the pre-disclosure, include the Linux Kernel, FreeBSD, NetBSD (used heavily in integrated devices), Mac OS X, Solaris, Novell Netware, FreeNAS, VERITAS, EMC, and NetApp. If these vendors are in fact impacted, without the same heads-up that Microsoft received, users of these products may be at increased risk when details are published and there are no patches available.
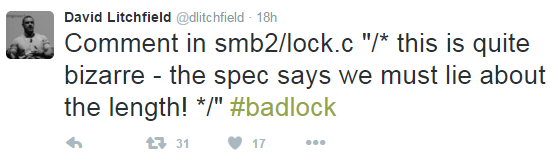
At present, the Samba web site still has the same brief blurb saying the information is coming, but no official statement regarding Metzmacher, Loxen, and SerNet’s involvement and handling of what is becoming a fiasco. We’re sure several journalists have reached out to Samba for a statement, but without an obvious single person as a designated leader, a statement may take a while to appear. More interesting is if the six Samba core developers that are part of SerNet will have their input into the process. Meanwhile, researchers are still pointing out interesting bits in the Samba code and further speculating on the vulnerability as more information becomes available. This speaks to a problem in the open source model, where some form of liability is difficult to place. For Samba, it comes in the form of so many core developers and no apparent unified voice that has a name. For libraries and smaller packages, sometimes finding an email contact or the official vendor page is near impossible.
Earlier today, Jake Williams posted his thoughts on Badlock, dubbing the ordeal a “douche disclosure” instead of the more friendly full disclosure, responsible disclosure or coordinated disclosure. He goes on to take exception with conspiracy theories that Metzmacher deliberately introduced the vulnerable code since this issue also affects Windows, where Metzmacher could not have introduced the code unless it was borrowed by Microsoft. That is absolutely a fair assessment and probably right. However, it does not mean that the vulnerable code wasn’t an accident, and still introduced by Metzmacher or one of the SerNet / Samba core developers.
The one thing most can agree on, is that the style of pre-disclosure taken by Metzmacher et al is not benefiting anyone but themselves and the company they work for. This isn’t a case where naming the vulnerability will help ‘force the vendor to patch’, since they are clear the patch is already in the works and coming soonish. While a researcher or company may want to capitalize on their efforts in finding the bug, that can be done much closer to the patch (including naming the vulnerability) being released to minimize the window of independent discovery. As it stands, even though this issues has gained a lot of exposure, Badlock has done nothing but put all organizations using SMB/CIFS at potential risk should the issue be figured out by criminal hackers, or a researcher who opts to share the details with the world.

Leave a Reply