Category: Technology
-
Mythos Needs to Shift Left

Over the years I have been part of many discussions around a classic debate around red team versus blue team, the value of penetration testing, and the value they each bring. I started my InfoSec career in 1996 doing pentesting (aka red teaming) a couple years before it really exploded. For nine years that was…
-
The Night I Almost Died

I write a lot. Most recently it has been about information security, movie reviews, so-called AI, and a few other topics. It’s been four years since I blogged about my poor experience with Abbott’s Libre2 glucose sensor technology and all the shortcomings. Since then I have tweeted to them a considerable amount when my continuous…
-
Why Data From So Many Breaches Never Sees the Light of Day
Months ago I was chatting with a colleague about a recent data leak (a.k.a. Data breach), as we tend to do in this industry. Those terms are defined by Microsoft as “an unauthorized disclosure of sensitive, confidential, or personal information from an organization’s systems or networks to an external party“. Any time I see an…
-
An AI agent destroyed … hey wait a minute!

Yesterday many people ran across a headline that was shocking, and repetitive. This time it read “‘Gone in 9 seconds’: Claude-powered AI agent deletes startup’s entire database“. For myself, the first thing I had to do was check the date of the article because I swore I had just read about this recently. Yep, April…
-
We Are Legion (We Are Bobservations); Answering a “Simple” Question

In late February, a friend linked an article about a science-fiction book and asked if I had read it. I told her that I hadn’t but after reading an abstract it sounded good. She asked if I would be her designated reader due to her workload, and report back. I said sure! She was particularly…
-
Windows 10 Fails

[This was originally started on 2021-03-07, adding notes from months before that. Given the time that has passed, I will not finish this but wanted to post my notes, as is.] windows is X years old, and despite the bloating and bugs, they still haven’t figured out some pretty basic UI/UX things. these are the…
-
Netflix: Why People Are Leaving You… (The Unspoken Reason?)

I can be long-winded in my blogs, I know, and there is a lot to unpack here. I’ll try to keep it brief. Famous last words =) Any Netflix engineers reading, it will be worth your time even if you skim fast. In the last month there has been global news coverage about Netflix losing…
-
Perlroth, Miller, and the First Remote iPhone Vuln
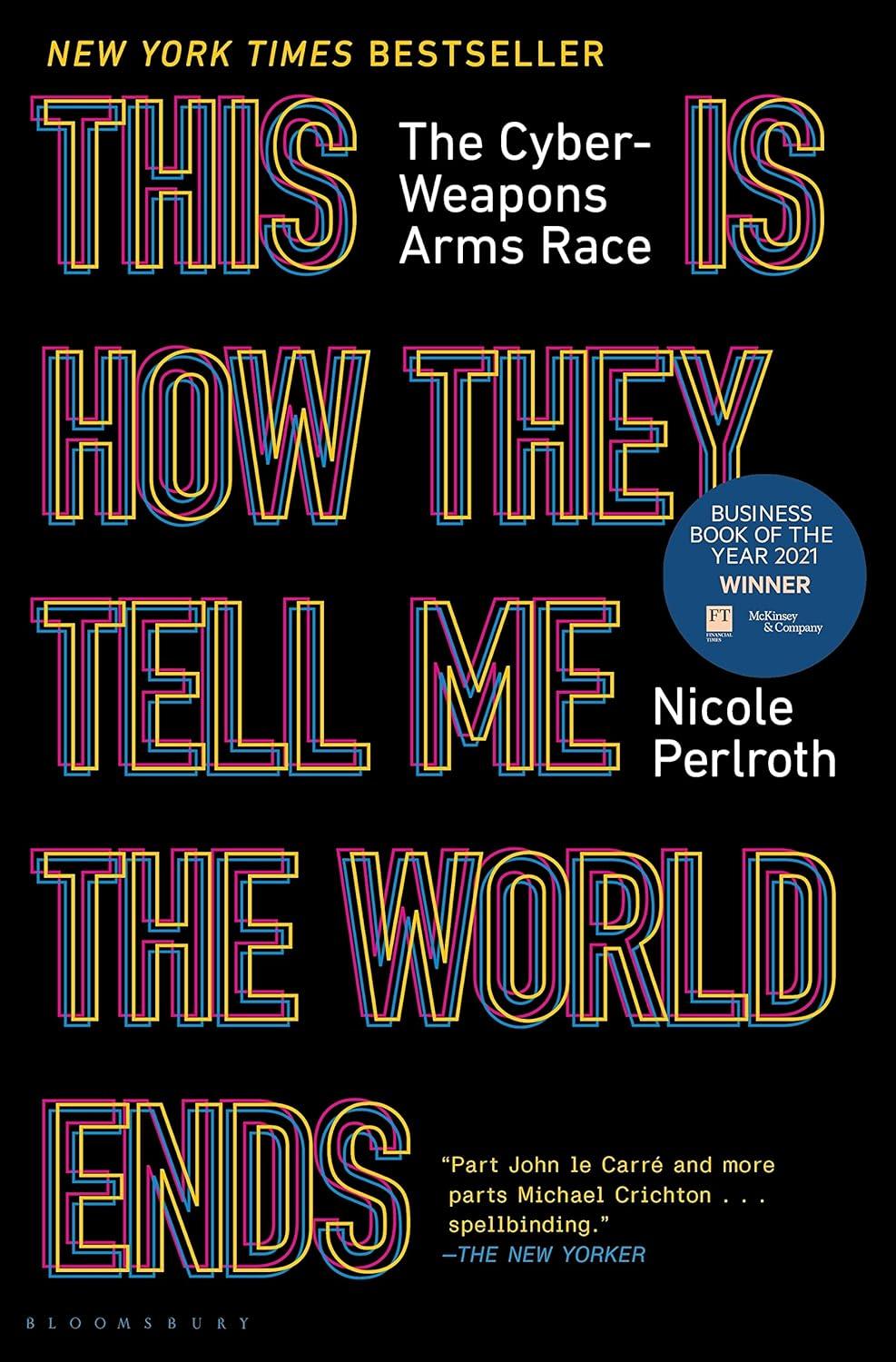
In what is sure to be my last blog (?!) born out of reading “This Is How They Tell Me The World Ends” by Nicole Perlroth, this article is basically a quick dive into a single paragraph that contains one sentence with an alleged fact pertaining to vulnerability history. As a self-described Vulnerability Historian, this…
-
My Photography is Popular
According to Ken Rockwell, via the first result of a Google search, the definition of a professional photographer is someone: .. who earns 100% of his income from photography. This is the definition required for entrance into the secret Nikon and Canon factory support organizations. People who earn less than 50% of their income from…
-
Search Speak for Automaton

Alternate titles for this blog could be “Doodle Transition for Machina” perhaps! For at least a decade I have thought about just such an application and today I have Google Translate for Android. Load, aim, and it will process the text and translate on screen for you. Given the state of technology you would think…