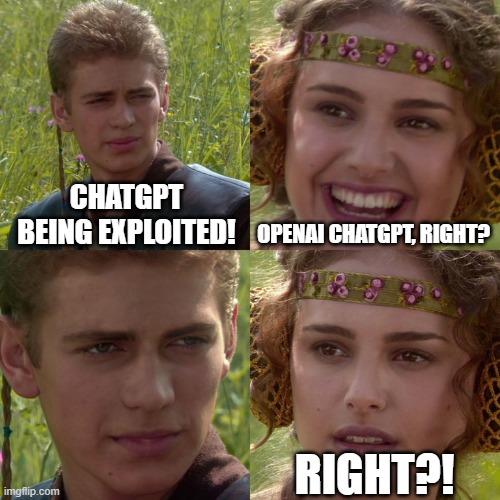
After years of chasing down typos in CVE IDs, now we all have to contend with poorly researched headlines and apparent to me ambulance chasing over mistaken product names. If you missed the news, threat actors are exploiting a vulnerability in ChatGPT! This is obviously a huge warning and we should all be afraid because of how prevalent ChatGPT is! Right?
Regular readers of mine will know what’s coming up next: Nope. First, let’s examine just two cases of how this is being blown out of proportion, and why. Note these are just two examples that I have seen, of many, and both are particularly egregious for different reasons, one because in my opinion it is basically ambulance chasing (something I historically don’t appreciate) on the back of this vulnerability, while the second is a considerable mistake from a news outlet I appreciate and respect.
The Lawyers
Quarles & Brady LLP, a large law firm with offices all over the United States, posted a newsletter on their site titled “Warning! ChatGPT Exploit Used by Threat Actors in Cyber Attacks“. In the article, Quarles & Brady raises the alarm over this vulnerability offering this recommendation:
Organizations should identify attempted or successful attacks, activate incident response plans, contact counsel to maintain privilege over investigations, and bring in internal and external experts sooner rather than later to support any necessary containment, assessment, and mitigation efforts as necessary.
[..]
For questions about this update or inquiries related to cybersecurity or artificial intelligence, please contact your Quarles attorney…

They go on to say they “will continue to monitor developments relating to potential vulnerabilities of AI technology.” What they do not say is that this vulnerability does not affect the ChatGPT you are likely thinking about. They seem to introduce brand confusion because someone overlooked the fact that this is not “Official ChatGPT from OpenAI“. Instead, this is “chatgpt” written by “dirk1983” and the software author describes it as “… a PHP version that calls OpenAI’s API interface for question-answering.” So this is a third-party interface to the official ChatpGPT. That means that dirk1983’s software is vulnerable, not OpenAI’s.

This is a critical distinction because the number of companies implementing OpenAI’s software is likely quite considerable these days. On the other hand, dirk1983’s software is likely less used, especially in the U.S. as the author is Chinese. The project currently has 814 forks and 3.2k stars so it is likely widely used, but also very likely widely used in China rather than the United States. Even looking at NVD, which Quarles & Brady reference but do not link to, it was made quite clear by January 21 who the vendor was.
Rather than consulting Quarles & Brady on “cybersecurity or artificial intelligence” like they suggest, perhaps OpenAI could consult with them if their newsletter is defamation per se. 😉
The Media

The second example that was particularly egregious was this Dark Reading article by Elizabeth Montalbano (mirror taken 3/23/25). While the law firm strongly implied the vendor was OpenAI via omission of details, Dark Reading makes it very clear they are reporting this vulnerability being exploited is in OpenAI’s ChatGPT itself, as seen in their header graphic above. To me, this is quite a surprise as Dark Reading’s reporting on vulnerabilities is usually very well done, well-cited, and provides good explanations of technical issues.
In the article, Montalbano specifically cites the vulnerability in OpenAI’s software rather than making the distinction it is in a third-party interface, saying researchers “from Veriti discovered the vulnerability in OpenAI’s ChatGPT infrastructure, which is tracked as CVE-2024-27564…” I emailed the journalist On March 20 pointing out this error and as of the time of this blog, the article is still incorrect.
Lessons Learned
Software naming collisions happen frequently enough, and have for decades. Veterans of InfoSec will remember confusion over “X Windows” at times, for example. Today, while so-called AI is all the rage, people will be prone to talk about it, glorify it, and report on it. Regardless, the most basic of due diligence must be performed when reporting on vulnerabilities. While NVD had made the distinction of vendors clear earlier this year, there are many times where vulnerabilities remain in their queue, awaiting analysis. If you are not sure about attributes of a vulnerability such as the vendor, product, or anything else, please reach out to your local InfoSec nerd. Most are more than happy to spend time to help.
I look forward to both Quarles & Bradley as well as Dark Reading to update their respective articles, and I will happily publish an updated note on this blog reflecting their fixes if someone reaches out.

Leave a Reply