[This was originally published on attrition.org. This is a rebuttal piece to Is There a Maturity Link Between Software Security Assurance, Bug Bounty Programs? (2010-12-16) by @wh1t3rabbit (Rafal Los).]
So what you have to ask yourself as an organization is this: Is the money we’re offering as a bug bounty higher in worth than what the black-market is paying for what is certainly an 0-day vulnerability which can be turned into an exploit? So can you convince the hackers to give up the bugs they find in your code for $x, rather than selling it on the black market, or using it for their own benefit? Good luck making that math work.
This outlook makes it abundantly clear that you do not understand vulnerabilities, the vulnerability market, or vulnerability history. You forget one huge factor in your equation above, that completely borks any of your own math.
You have this delusion that one person can find one vulnerability and then it somehow locked, and no one else can find it. As if there are no other quality vulnerability researchers out there, or if there are, they simply aren’t looking. Back between 2000 and 2004, VDBs noticed a significant increase in multiple security companies discovering the same exact vulnerability (typically remote code execution), and each one coordinating with disclosure. Take for example the “RealPlayer embd3260.dll URL Parsing Overflow” from 2004/06/10. A context-dependent (typically remote) code execution vulnerability discovered by eEye, iDefense, and NGSSoftware simultaneously. If researchers from all three of those discovered the issue at the same time, you have to assume that additional researchers were just as likely to discover it. More to the point, that means any black hat types were also just as likely, and just as capable.
The point of a bug bounty program isn’t just about this bad math you have in mind. First, you miss that a legitimate security shop doesn’t shop around on these vulnerabilities usually. If they do, it is between other legitimate vulnerability brokers (e.g. iDefense, ZDI) and/or the vendor’s bug bounty. They don’t shop it around to the “black-market” as you suggest. Second, you made this really stupid leap to “hackers” being the ones to find vulnerabilities, and forgot about the entire researcher community. That leads into a variety of motives you completely missed, including the easy no-hassle and no-risk sale to the vendor, and the chance to get their name in a high-profile vendor’s blog as finding a serious security vulnerability in their product. If you think for a minute that isn’t valuable, you miss why most companies release formal advisories after coordinated disclosure. It is pure resume fodder, and it is extremely valuable.
So the simple point is, the bug bounty encourages legitimate researchers to keep sending them vulnerabilities, to be fixed and disclosed on their timetable. For every vulnerability a legitimate researcher kills, the “black-market” has lost a 0-day. To summarize, a bug bounty may or may not represent a certain amount of maturity in the assurance cycle, but it is a valuable tool in killing vulnerabilities. In case you have any doubts about what I say, I will leave you with this article about Google paying someone US$60,000 for a vulnerability. Does that compete with your “black-market”? Yes, it does.
Does it mean that Google, Microsoft and Mozilla are anomalies in our industry? Probably.
Probably? Even at the time of this blog post there were considerably more companies doing bug bounties, one going back some 15 years (Netscape). Some programs were instituted since your blog post, but I believe this just demonstrates you failed to predict the value of bug bounty programs since they are increasing. Many bigger vendors are doing it: Google, Google Chromium, Mozilla, Barracuda Networks, Yandex, and AT&T for example.
Then we have a variety of web sites / services offering bounties: PayPal, CCBill, Facebook, Etsy, Google Gmail.com / YouTube.com / Blogger.com, and Ishar to name a few.
Even smaller institutions like schools are offering it, like Rotan Independent School District and JW Hayes Primary School (and many others offered by Tennant & Associates).
Software bug bounties are not limited to the big players either, as we see from smaller shops: Piwik, Gallery, GhostScript, Samsung TV, Mahara (ended), Tarsnap, Hex-Rays, Kaneva, and SynringePumpPro.
The idea of bug bounties has even extended to books recently: CommonsWare.
And finally, don’t forget third parties that will pay for bugs: Secunia, Verisign iDefense, HP / TippingPoint ZDI, and iSight Partners.
Finally, your “How Finding Bugs in Software REALLY Works” flow-chart is not well thought out:
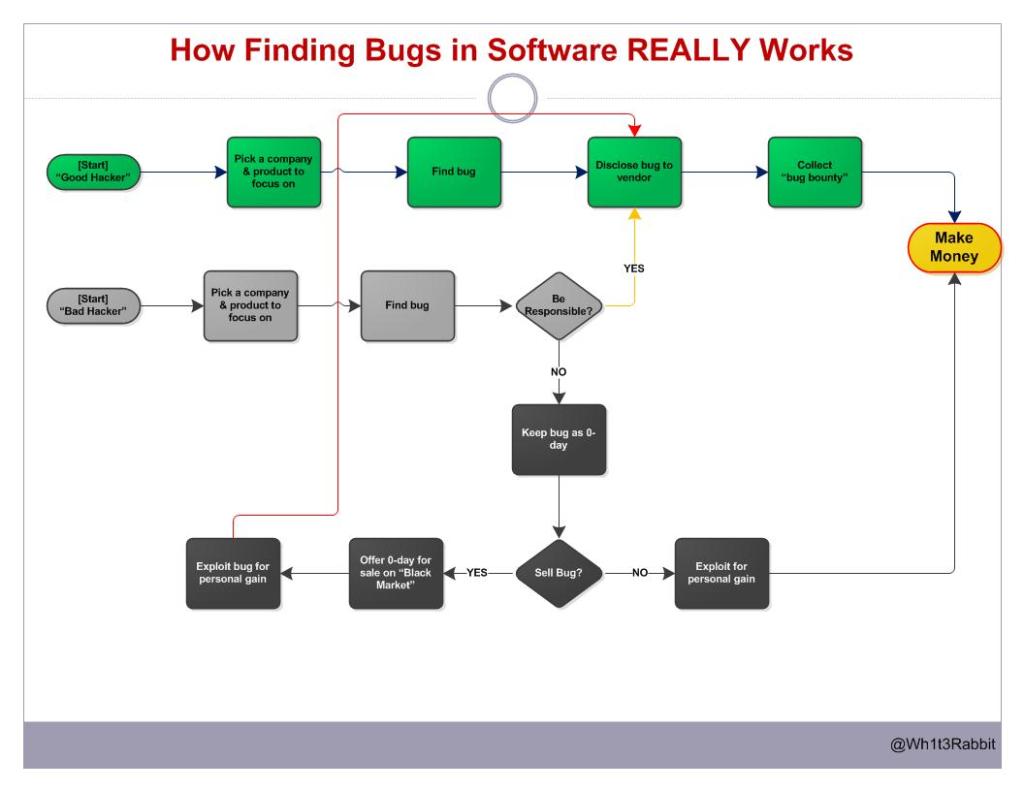
Bad Hacker – Pick A Company – Find Bug – Be Responsible (No) – Keep bug as 0-day – Sell Bug (Yes) – Offer 0-day for sale on Black Market – Exploit bug for personal gain – Disclose Bug to Vendor – Collect Bug Bounty – Make Money
I do not believe this is a common scenario for black hat hackers at all. In the process of exploiting as many hosts before the vulnerability is discovered (via any means), it makes no sense to give up a vulnerability unless doing so is more profitable. That happens when all hosts have been exploited, or most hosts have been patched against the flaw, meaning the vulnerability is already burned and likely not to be accepted via the bug bounty. I am sure some will ‘double-dip’, either selling it to multiple programs, multiple black-market buyers, and/or personally use it for gain, but defining the above as an absolute and saying that is how it REALLY works is short-sighted and very shallow. Finally, look at your chart. Before that entire process goes down, you have an option “Be Responsible?” which diverts into two opposite directions. Yet the ultimate result is the same for “be responsible” and “don’t be responsible”? Not very logical.
Leave a Reply