[This was originally published on RiskBasedSecurity.com.]
On April 18, 2018, vpnMentor disclosed a ‘critical’ vulnerability in LG NAS devices, which also received a bit of media attention. The blog leads with “Here at vpnMentor, we are concerned about your security and privacy.”
However, that didn’t seem to apply to a specific system in South Korea. In their blog, they include a video demonstrating the exploitation technique. Unfortunately, they failed to obscure the IP address of the system they tested in half a dozen instances. Basically, whatever tool they use to blur the IP address wasn’t started in time, showing the real IP before it kicks in, and then subsequently any time the URL history drop-down in their browser retracts, briefly showing the un-obscured URLs including payloads for their attacks.
While aggregating vulnerabilities for VulnDB for a number of years, it has become more common for us to see researchers of all varieties test live systems like this. Typically, but not always, that doesn’t include legitimate companies, who advertise privacy and security. When confronted on Twitter about this, vpnMentor denied the allegation saying the IP was a decoy. Yes, they did include a decoy IP address in the video, but that wasn’t the one being tested and subsequently leaked in their disclosure. The video goes on to show the researchers exploiting a remote, unauthenticated command injection vulnerability in the login form of the LG NAS device to upload a backdoor. This is exploited to e.g. dump the users and create a new user account, which they then use to log into the NAS device.
Curiosity got the best of us, so we checked, who owned the decoy IP address (shown in a screenshot of Burp proxy software) as well as the IP of the device they were testing (shown in the browser they used) against – or rather outright compromised. The decoy IP is registered to the Netherlands and did not answer on TCP port 8000, while the tested IP is registered in South Korea and responded to a request. Loading that IP in a browser showed us the same LG device interface as the video. Making a request to the custom file they wrote to the device further verified it was indeed the device from the video. We point all of this out as another reminder that while finding and disclosing vulnerabilities can have a lot of value, doing it while testing against systems without permission is dangerous to both sides.
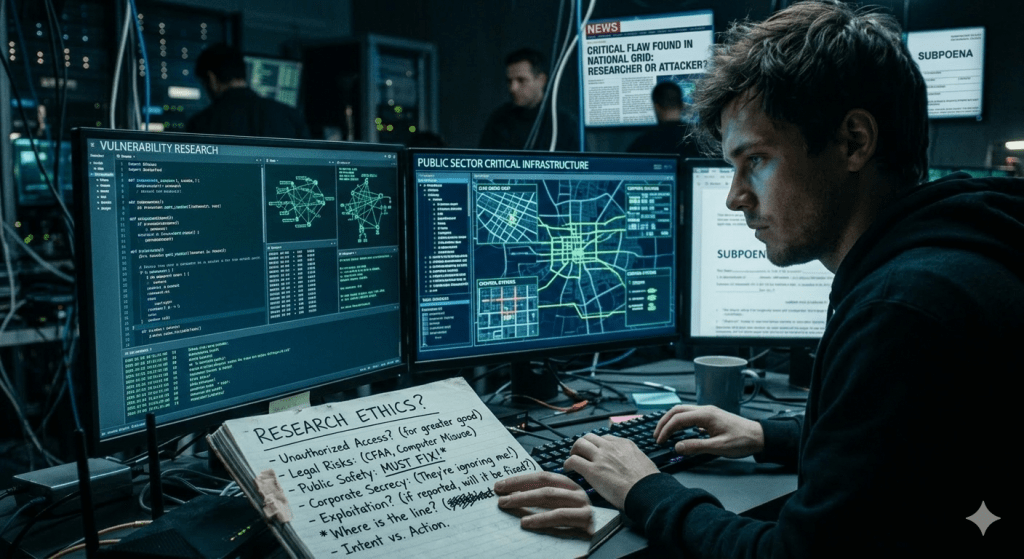
In fact, while are not asserting malicious intent, let us call it what it is: It is not “testing” but outright “hacking”. A device is being compromised without prior consent by the owner. It is not only unethical, but as a researcher, you are most likely violating numerous computer crime laws where you live.
Your testing may also end up crashing or have other negative impacts on a system that is considered critical by the target organization. While we all agree that critical systems should not be Internet-facing, we also know the reality that plenty are. The balance between vulnerability research into software and the legal issues is a very fine line.
However, reporting vulnerabilities in Internet-connected systems or data breaches to organizations has been a real problem recently leading to researchers facing serious consequences. For example, consider the case of Justin Shafer, a security researcher who found himself being raided by the F.B.I. after discovering the sensitive patient data of 22,000 people on a public server. He is now facing possible prosecution under the Computer Fraud and Abuse Act (CFAA). Shafer’s case is a good reminder of the activity pointed out earlier, where a researcher interacted with and tested a live system on the Internet. Even with the best of intentions, that still runs afoul of the law in many countries.
In the United States, researchers now face a new nightmare, where states are imposing considerably more draconian laws regarding computer crime. This is best observed with the recent legislation passed in Georgia, State Senate Bill 315, titled “Computer Crimes; create a new crime of unauthorized computer access”. The legislation, which the EFF calls “anti-InfoSec” creates severe penalties, could make the best of intentioned researchers who disclose vulnerabilities in systems face prosecution and up to a year in jail. Given the wide variety of hardware and software out there, and how inexpensive a lot of it is, it is much safer for all parties to find a used system online and purchase it.
Not only does this help you avoid any legal or ethical issues, it gives you even greater access to the device to perform more in-depth testing. With that, you are likely to find additional vulnerabilities that you may not have been able to before. In the case of the LG NAS disclosure, a similar device can be found on eBay for less than $100 right now. If a given piece of software is out of your budget, ask around or even the vendor might be willing to provide a device for testing. Working together in that way strengthens the Information Security community in more than one way. RBS has reached out to the owners of the “tested” device to notify them that it was compromised and that it should not be Internet-accessible.